Enterprise Risk Management and Internals Controls
The Company recognizes the increasing importance of sound risk management practices to drive business growth and sustainability. The Company implemented systems and processes to facilitate proper risk identification, monitoring and control, which are key to effective corporate governance. Timely and accurate management and financial reporting systems, internal controls, and audits are also employed to protect and maximize stakeholders’ value.
The Board oversees Management’s adoption and implementation of a sound risk management framework for identifying, monitoring and managing key risk areas. The Board reviews the risk management framework annually to ensure its continued relevance and effectiveness.
Enterprise Risk Management (“ERM”)
The role of ERM is to ensure that a sound ERM framework is in place to effectively identify, monitor, assess and manage key business risks. The risk management framework shall guide the Board in identifying units/business lines and enterprise-level risk exposures, as well as the effectiveness of risk management strategies.
Risk Governance
The following structure represents the line of responsibility of key functions that ensure the effective management of all risks that are considered material to the Company.
The Board of Directors (BOD) assumes ultimate responsibility for the oversight of the Company’s ERM policies and procedures. The BOD sets clear directions on the management of the most important risks and evaluates the overall effectiveness of the ERM process, both at the operating company level and the JGSHI level. The Board of Directors reviews Management reports with due diligence to enable the Company to anticipate, minimize, control and manage risks or possible threats to its operational and financial viability.
The Audit, Related Party Transactions and Risk Oversight Committee (AURROC) oversees the implementation of the ERM plan in accordance with the Board approved policies and procedures and it ensures the Board is fully informed on material risk exposures, mitigation actions, and residual risks.
The Chief Finance and Risk Officer (“CFRO”) leads the Enterprise Risk Management process that will ensure a sound ERM framework is in place to effectively identify, monitor, assess and manage key business risks. The CRO spearheads the development, implementation, maintenance and continuous improvement of ERM processes and documentations, and communicates significant risk exposures, control issues, and risk management plans to the AURROC. Under the risk and controls function, the CFRO is the steward of risk management, specifically those that have financial impact and affect company value.
 Brian M. Go, 50, was appointed as the CFRO of JGSHI on July 1, 2021. He is also a Board Director and Executive Committee member for Maxicare, Maxilife and Maxicare Health Services, the Managing Director of URC Equity Ventures Pte Ltd., as well as serving on the Investment Committee of JG Digital Equity Ventures (“JGDEV”), and a Senior Advisory Board member of Robinsons Bank Corporation. Brian started his career in New York City with Booz Allen Hamilton in 1996, in the Financial Services practice. He returned to Manila in 1998, working at DTPI (Digitel/Sun Cellular) in Corporate Planning, and as Managing Director of the Datacom business. He worked in China from 2003 to 2013, serving as Finance Director, then Chief Financial Officer of Ding Feng Real Estate (DFRE) group of companies. From 2007, he concurrently assumed the General Manager role for URC China, and was later appointed General Manager of URC Malaysia/Singapore. He was also the Vice President for URC’s International Trading Operations/Global Exports based in Singapore from 2019 to 2022. Brian graduated from Harvard University with a degree in BA Economics, Cum Laude, in 1996. He completed his Executive MBA with Kellogg-HKUST in 2007 and is a CFA charter holder.
Brian M. Go, 50, was appointed as the CFRO of JGSHI on July 1, 2021. He is also a Board Director and Executive Committee member for Maxicare, Maxilife and Maxicare Health Services, the Managing Director of URC Equity Ventures Pte Ltd., as well as serving on the Investment Committee of JG Digital Equity Ventures (“JGDEV”), and a Senior Advisory Board member of Robinsons Bank Corporation. Brian started his career in New York City with Booz Allen Hamilton in 1996, in the Financial Services practice. He returned to Manila in 1998, working at DTPI (Digitel/Sun Cellular) in Corporate Planning, and as Managing Director of the Datacom business. He worked in China from 2003 to 2013, serving as Finance Director, then Chief Financial Officer of Ding Feng Real Estate (DFRE) group of companies. From 2007, he concurrently assumed the General Manager role for URC China, and was later appointed General Manager of URC Malaysia/Singapore. He was also the Vice President for URC’s International Trading Operations/Global Exports based in Singapore from 2019 to 2022. Brian graduated from Harvard University with a degree in BA Economics, Cum Laude, in 1996. He completed his Executive MBA with Kellogg-HKUST in 2007 and is a CFA charter holder.
The Risk Council supports the CRO in identifying key risk exposures in all areas, including those relating to Economic, Environmental, Social and Governance factors and defining risk management strategies. The Risk Council leads the development of risk mitigation plans and in monitoring risks and effectiveness of response plans.
Risk Champions are functional or business unit heads responsible for setting and implementing controls to mitigate risks relevant to their respective departments or business units. They act as the ERM subject-matter experts on specific risk categories and collaborate with other risk champions to better understand risk interaction across the organization. They ensure the effective execution and continuous improvement of the ERM process in their respective areas of responsibility.
The Risk Owners are directly accountable and responsible for the identification and management of assigned risks. They work with risk champions to determine the best approaches to managing the risks. They evaluate the effectiveness of response, track and report residual risks, and recommend further risk treatment to the risk champion and the ERM Team.
Internal Audit provides independent assessments to the AURROC, Management and outside parties on the adequacy and effectiveness of governance, risk management, and control processes for the Company.
Risk Management Process
The Company acknowledges that viewing business risks and opportunities that includes the context of sustainable development challenges is the way to remain responsive, risk intelligent, relevant and successful. In 2021, JGSHI identified key risk owners and risks in each operating company and the Corporate Center Unit and provided them with the needed tools to conduct more comprehensive risk identification process, assessment, and prioritization. The Company engaged Business for Sustainability Development (BSD) to help facilitate this process and enhance the Company’s ERM system to better capture Sustainability risks, formulate mitigation and response, and improve risk disclosures.
The risk management process employs a bottoms-up approach. The top risks for each functional unit were rolled up to the enterprise level of each operating company and further elevated to the JGSHI level. The Group’s top risks and mitigation plans are regularly reported to the AURROC.
Every year, the Company discloses the top risks in its Annual Report.
Risk Identification, Assessment, and Prioritization
Risk champions and owners conduct risk identification using different tools such as risk factor analysis, megatrends analysis, and systems dynamics analysis. This enables them to determine the factors that could prevent delivery of their unit’s business objectives. Identified risks are grouped into categories as follows:
a. Strategic risk concerns events that could affect the outcome of strategic decisions, such as mergers and acquisitions, key investments, resource allocations, and new business ventures.
b. Reputational risk refers to anything that could impact the company’s brand value, public perception, and stakeholder relationships.
c. Governance risk pertains to risks related to implementation of and adherence to policies and procedures and ethical practices within the organization.
d. Emerging risk refers to new or developing risks that the company has little to no experience in, such as climate change, biodiversity loss, and pandemics.
e. Climate Risk refers to potential physical risks that may arise from climatic events or business risks arising from regulatory efforts or changing stakeholder expectations associated with the shift towards a carbon-neutral economy.
f. Operational risk relates to factors that could potentially disrupt routine business activities or impair property, infrastructure, and security.
g. IT and Digitalization risk refers to the risk of business disruption which may be caused by hardware or software failure, cyberattacks, unauthorized access to company information, and the like, or lost opportunities associated with lack of innovation or investments in technology.
h. People risk refers to factors and events that could compromise the wellbeing, productivity, and performance of our workers.
i. Financial risk refers to matters that could affect the financial position or performance of the company such as credit, liquidity, and foreign currency risks.
j. Legal and Compliance risk includes risks related to compliance to rules and regulations, adaption to changing political landscapes and new government pronouncements, as well as exposures that could arise from contractual obligations, anti-competition and monopolization concerns, and legal disputes against the company.
For each risk category, an impact assessment scale is developed that defines what is considered insignificant, minor, moderate, major, or extreme impact to the business. Likewise, likelihood parameters are set defining whether the chance of occurrence is rare, unlikely, probable, likely, or almost certain. The risk assessment scale is developed in the operating unit’s business context and risk appetite.
In assessing risks, the severity of impacts of the risks is rated based on their nature, regardless of the organization’s circumstances and capability to manage them. Those rated high and very high in severity are considered in the prioritization process.
Risks are prioritized based on our organization’s risk profile, vulnerability, and contribution to aggravating certain risks. The latter is particularly relevant to ESG risks, like climate change impacts which the Company also contributes to. Furthermore, the Company also considers the urgency of the risks which is a factor of velocity or how quickly the impact of the risks is felt when they materialize, and the mitigation timeframe or the length of time needed to manage these risks.
Risk Response, Monitoring, and Evaluation
The Company ensures that appropriate risk responses are in place for each priority risk, both at the level of the risk champions and risk owners and at the enterprise level of the operating companies. Risk responses have also been put in place at the JGSHI level, specifically those that are common across the Group.
Risk champions are tasked to continually monitor and evaluate the effectiveness of the risk responses. Material residual risks are assessed properly for improvement of risk response and identification of recovery measures.
Given the dynamic nature of risks, the entire risk management process is iterated as separate and independent process at the functional units of the operating companies and as a group-wide process.
IT Risk Governance
JGSHI recognizes that Cybersecurity controls are an essential component of any organization's overall security posture. The Company follows well known Cybersecurity frameworks such as National Institute of Standards and Technology (NIST) and International Organization for Standardization (ISO). The Company adheres to the following principles and best practices on security controls:
- A layered approach to security controls is used to protect the organization's assets. This includes physical security measures, such as access controls and surveillance cameras, as well as technical controls, such as firewalls, intrusion detection systems, and endpoint protection software. The layered approach creates a more robust and effective security system.
- Regular testing and monitoring of security controls is conducted to ensure their effectiveness. This involves conducting penetration testing, vulnerability scanning, and other types of security assessments to identify weaknesses in the security system. Regular monitoring of security logs and alerts also helps detect potential security incidents before they become serious threats. This process allows the Company to identify and address weaknesses in the security system, thereby reducing the risk of a successful cyberattack or data breach.
Effective management and reporting of identified security risks require a proactive and collaborative approach across the organization. JG Summit Information Security Office (JGS ISO) regularly reviews and updates risk management practices to adapt to the evolving threat landscape and changes within the organization.
To effectively manage and report identified cyber security risks, JGS ISO adheres to the following best practices:
- Prioritize identified security risks based on their potential impact and likelihood of occurrence and focuses on addressing high-priority risks first to mitigate the most significant threats to the conglomerate.
- Develop and implement risk mitigation strategies for each identified risk. Determine appropriate controls, safeguards, and countermeasures to reduce the likelihood and impact of the risks. Align these strategies with industry best practices, regulatory requirements, and to the organization's risk appetite.
- Information Security Incident Response Plan that outlines the steps to be taken in the event of a security incident related to the identified risks. Define roles and responsibilities, communication channels, and escalation procedures. Regularly test and update the plan to ensure its effectiveness.
- A continuous monitoring program to detect and respond to security incidents and changes in risk levels. Monitor security controls, conduct vulnerability assessments, and analyze security logs and alerts. Proactively identify and address emerging risks and vulnerabilities.
- Establishment of a robust reporting mechanism to communicate identified security risks to relevant stakeholders. Prepare clear and concise risk reports that provide an overview of the risks, their potential impact, and the status of risk mitigation efforts.
- Define clear and relevant metrics and KPIs to measure the effectiveness of your risk management efforts. Track and report on these metrics regularly to assess the progress in mitigating identified risks. This helps in demonstrating the organization's commitment to security and provides insights for continuous improvement.
- Conduct periodic risk reviews to reassess identified risks, evaluate the effectiveness of risk mitigation strategies, and identify emerging risks. Incorporate feedback from security incidents, audits, and assessments into the risk management process. Use the findings to refine risk mitigation strategies and enhance security controls.
- Educate employees about the identified security risks, their potential impact, and their role in mitigating those risks. Provide regular training sessions and awareness programs to promote a culture of security within the organization. Encourage employees to report security incidents or potential risks promptly.
Risk Disclosures
The group’s risk register undergoes a periodic review to ensure that it captures the relevant risks that can potentially affect the business. Risks that are rated high are deliberated by the Risk Council as to their potential impact to the various aspect of the business, taking into consideration existing controls and mitigation measures, as well as, the Group’s risk appetite and perceived vulnerabilities. The following are considered the top risks for the Group:
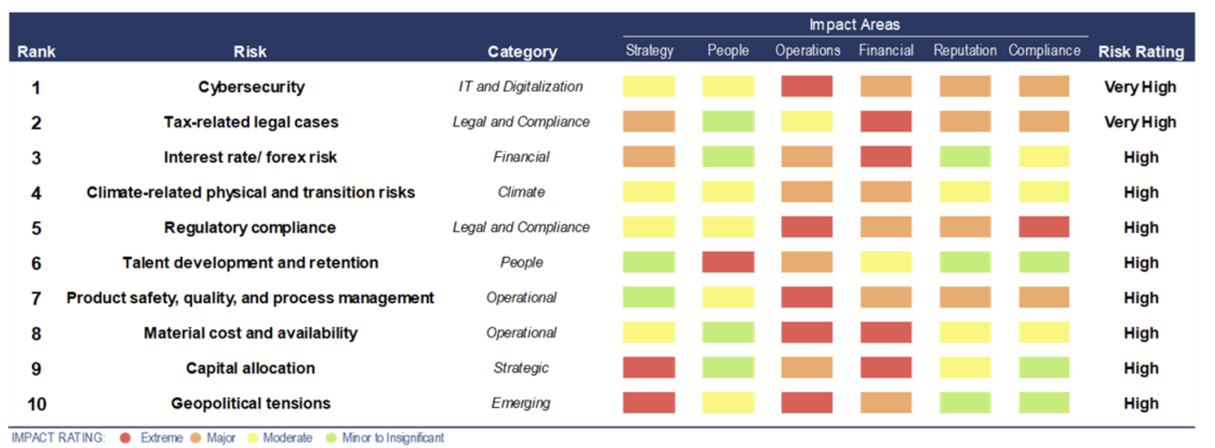
The Group considers cybersecurity as its top risk, under IT and Digitalization, due to the severity of its potential impact to the Group’s operations. The consequences related to this risk include possible loss of information, disruptions in business operations, increased cost of added security or disaster recovery, and potential loss of credibility and damage to brand and company image. This risk could also lead to significant regulatory violations. Data breaches could compromise the Company’s sensitive or confidential information, and even jeopardize individuals’ safety and security, in case of personal data leaks. We are actively mitigating this risk as we continue to strengthen our security posture with pragmatic and holistic solutions to proactively identify, protect, detect, respond and recover, as well as improve our system and data access controls. Actual cybersecurity incidents and their impact are investigated, resolved and reported to the business unit management and Data Privacy Officer, in case of data security breaches.
Our top Legal and Compliance risks include tax-related legal cases and non-compliance with regulations. Non-compliance with any law, including environmental regulations, could have financial and reputational implications for the Company from fines to stoppage of operations. We are closely monitoring regulatory updates such as those related to the Single-Use Plastic Products bill, the Extended Producer Responsibility Act and carbon emission-related policies. We have a team of in-house legal experts who coordinate with concerned business units on potential legal issues and pursue all remedies available. We also engage with third-party consultants, as necessary, to strengthen our position on related issues. Our Company ensures that the Group maintains compliance with regulatory requirements.
Our main Financial risks are related to interest rate increases and foreign exchange volatility, which could significantly impact our Group’s financial performance. Possible effects include higher cost of debt, lower returns from financial investments and margin compression from higher input costs. To counter this financial risk, our Group manages and maintains a good balance of foreign-denominated financial assets, local currency borrowings, risk-appropriate instruments, while strengthening both our onshore and offshore banking relationships.
Climate-related risk is considered one of the most relevant risks for the Group. The inability to mitigate or address the impact of climate-related and extreme weather events could result in damage to facilities, obsolescence or loss of assets, disruptions in the Group’s supply chain and operations, as well as, endanger people and the ecosystem. Enhancing infrastructure resilience against extreme weather events and adapting to changing conditions could require significant financial and capital investments. Regulatory changes related to climate change, such as carbon pricing, emissions caps, and extended producer responsibility, may also affect the Group operationally and financially by escalating compliance costs.
This year we embarked on a project to gain better understanding of science-based climate risks information from the best available climate models to understand how our facilities and value chains can get impacted under different climate scenarios. See “Climate Disclosure Report” portion of this Sustainability Report.
On People risk, talent development and retention remain to be crucial in the face of intense competition for key talents, especially for those with digital aptitude. High attrition could result in business disruptions, compromised service quality and increased cost of talent acquisition and training. In order to address these risks, we continually upgrade our talent acquisition strategies, conduct wages and benefits benchmarking, and employ data insights and advanced analytics in developing HR programs for employees’ professional growth and development.
We foster a safe environment for labor unions to freely communicate their concerns to the management. This is key to arriving at a mutually beneficial agreement. When disagreements are not addressed immediately, the Company recognizes that it may run the risk of labor unrest, which can disrupt the company’s operations and ability to meet its customer’s needs.
A more diverse workforce could also improve the way the Company assesses the needs of its stakeholders. This opens the opportunity to innovate to better serve the needs of its stakeholders. This could alleviate exclusion of certain segments of the population, lower talent selection pool and high opportunity cost from untapped markets.
Our Company continues to work towards ensuring that employees are healthy and safe because we understand the consequences to life and property if this is not addressed properly. Noncompliance with health and safety standards and regulations could also cost the Company penalties from regulators, suspension of operations, attrition, and damage to reputation.
Product safety, quality, and equipment and process management concerns are among the Group’s top operational risks, along with risks of increasing material costs and availability. Rising raw material costs could negatively impact margins, while unreliability of raw materials supply could result in operational disruptions and loss of sales. The quality of our products and services, on the other hand, influences our relationship with our customers and their perception of the company. We are, however, always on top of these risks as we ensure that proper operations management and product quality management systems are in place, and there is diversity in raw materials sourcing and adequate insurance coverage for facilities, assets, and people. We have a supplier accreditation system in place to ensure continuous supply of quality goods and services by reputable and reliable suppliers who are compliant with applicable government rules and regulations like environmental, labor, health and safety, etc. To the extent possible, the Company promotes inclusive business in its value chain by getting supplies from farmers and cooperatives to provide employment and revenues to low-income communities.
By recognizing the potential for material scarcity, our Company is taking steps to reduce its reliance on non-renewable materials and adopt sustainable sourcing practices. This can include measures such as using recycled materials, reducing material waste through better design and production processes, and sourcing materials from suppliers that follow sustainable practices. Our Company also recognizes the potential risks to human health and the environment, posed by air emissions, air pollutants, and solid waste, and is taking steps to manage them responsibly. We are implementing measures to reduce these emissions, such as improving combustion efficiency or using lowemission fuels to help mitigate these risks. Similarly, solid waste can also have negative impacts on the environment and surrounding communities, if not properly managed, such as that of plastic waste. By adopting responsible waste management practices, such as reducing waste generation through better design or recycling and treating waste, our Company can help to minimize these risks. It is also important to address the potential for leakages in the waste management system, as these can lead to various hazards. By implementing measures to prevent and detect leaks, such as regular maintenance and monitoring, our Company can reduce the likelihood of these hazards occurring and protect the environment and surrounding communities.
Our top Strategic risk cover areas of capital allocation, business performance and competition. This relates to how our long-term portfolio investment decisions based on available information may yield lower-than-expected returns. Correspondingly, the perceived exposure of the Group to industry disruptions, market volatilities, geopolitical risks and ESG risks may affect stakeholder value. These risks could affect the Company’s market capitalization, or pose an unfavorable view in the Group’s value creation, and limit growth prospects. Our risk responses include conducting sector analysis in relation to customer trends, incorporating risk management in implementing the OGSM process in our businesses, regular review of capital allocation decisions and analysis on the potential impact on the parent company’s risk return profile, and effective communication of our business performance, as well as sustainability practices and initiatives.
For Emerging risks, we consider geopolitical tensions as one of our risks with the continuing conflict in the global order causing economic volatility and severely affecting the international commerce and flow of goods and labor. Potential impact to the Company includes difficulty in sourcing raw materials, decreased profits due to higher input costs, and reduced growth prospects. We incorporate geopolitical risk analysis and strategic foresight planning in market and transaction evaluation to reduce the impact of this risk. Furthermore, the Group is also assessing the impact of disruptive technology, such as Generative AI, in business operations. The possible implications include reduced competitive advantage from inability to capitalize on emerging technologies, and increased cost of equipping the organization to adapt to changing business landscape. We are working on developing Gen AI policies and setting up a governance committee to establish comprehensive risk management protocols and foster ethical and strategic use of Gen AI to enhance business processes, products and services.
Our Reputational risk pertains to how third-party views and ratings affect our corporate image and brands. Misinformation about JGSHI and/or its subsidiaries and unfavorable public opinion could impact the Company’s social license to operate, as well as market capitalization. We perform active scanning of mainstream social media outlets and continuously monitor our business positioning in the market and external reputation.
Our Company also follows a strict protocol in obtaining a social license to operate whenever it enters a certain community. Communities are important stakeholders who help the Company succeed. JGSHI recognizes risks related to poor community engagement, where communities’ concerns are not properly addressed, could push the community to act against the Company’s interest. It is crucial for JGSHI that the community understands the value that it brings to the community, and that the Company is open to hearing their feedback and doing what is best to address their concerns.
JGSHI also recognizes that unresolved customer complaints, especially when these reach digital platforms, may influence wider customer perception of the quality of our products and services. Issues surrounding product safety and quality, customer privacy and advertising, if remained unresolved, could lead to a decrease in customer satisfaction. Unmet customer satisfaction could result in a decline in sales, and eventual loss of market share. To ensure better customer experience, we strive to continuously improve our customer care platforms in terms of accessibility and responsiveness to achieve quicker resolution of customer concerns.
Our Governance risk relates to compliance with company policies and processes. Unintended or intentional breaches of company policies and ethical standards may result in operational inefficiencies, significant financial losses, loss of stakeholder trust, or reputational damage. Additionally, issues on corruption could compromise the Company’s ability to equitably distribute economic value to the right stakeholders. We address this by strengthening our internal control measures and functions. We also reinforce good corporate governance practices and regularly conduct training on code of business conduct and ethics. Our Company has anti-corruption policies and procedures in place such as a code of conduct that prohibits corrupt practices, and a reporting mechanism for whistleblowers to report any suspected corruption.

